A New Say in Secrecy: Congress Takes Up Classification Reform
Following fresh scrutiny of the U.S. classification system, Congress eyes new ideas and a new role in the regulation of national secrets.
Following several high-profile incidents involving classified material over the past year, Congress has taken on a formidable problem—reform of the U.S. government’s “byzantine, bureaucratic, and outmoded” system for classifying sensitive information and declassifying those secrets that no longer need protection. The alleged unlawful retention and transmittal of national defense information by an Air National Guardsman over Discord, and the recent discovery of classified material in the possession of the most senior executive branch officials after they had departed their posts, have prompted debate about the potential compromise of sensitive information as well as the gaps in the classification system that allowed these incidents to happen at all. The related issue of overclassification has made it more difficult for government agencies to share information and, as Director of National Intelligence (DNI) Avril Haines observed in a keynote address in January, undermines democratic objectives of transparency and accountability.
In May, members of the Senate Select Intelligence Committee (SSCI) introduced bipartisan legislation to address these challenges: the Classification Reform Act of 2023 (S.1541), sponsored by Sen. Mark Warner (D-Va.), and the Sensible Classification Act of 2023 (S.1518), sponsored by Sen. John Cornyn (R-Texas). House Permanent Select Committee on Intelligence (HPSCI) members Rep. Brad Wenstrup (R-Ohio) and Rep. Abigail Spanberger (D-Va.) introduced their own companion legislation, the Sensible Classification Act, H.R.5977, in October. The reforms contained in the bills seek to reduce overclassification, prevent mishandling of classified information, promote better use of intelligence, and enhance public trust. Although the precise means for achieving these goals have been materially revised in the version of the National Defense Authorization Act (NDAA) currently working its way through Congress, the proposed legislation is a clear message from both parties that Congress is ready to play a productive role in improving the system for classifying and declassifying sensitive material. By taking legislative action, Congress also is signaling that it believes it has a role in this system and that the classification apparatus should no longer remain within the exclusive purview of the executive branch.
The Limited, Historical Role of Congress in Classification
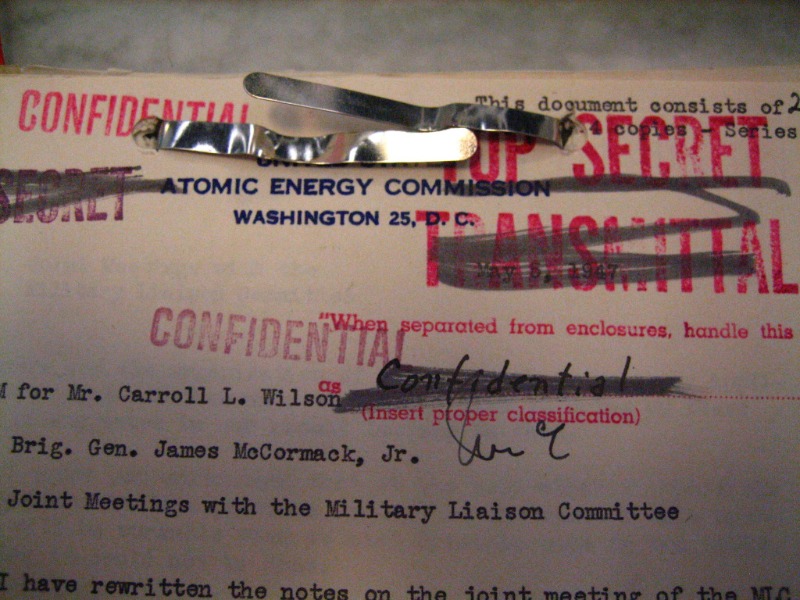
With the exception of early laws criminalizing the dissemination of national secrets and the Atomic Energy Act, which established categories of “restricted data” subject to classification, the modern system for classifying national security information has largely been governed pursuant to a series of executive orders (EOs) issued by presidents. In Department of the Navy v. Egan (1988), the Supreme Court recognized that the executive branch’s power over classified material is rooted in the Constitution, noting that the president’s “authority to classify and control access to information bearing on national security ... flows primarily from this constitutional investment of power in the President, and exists quite apart from any explicit congressional grant.” Executive branch officials have repeatedly invoked this decision, which concerned an appeal of a Navy laborer’s security clearance denial, as confirmation of the executive’s sole ownership of this subject, despite qualifying language elsewhere in the decision that some scholars have suggested implicitly recognizes Congress’s ability to legislate in this space. (See Egan, 484 U.S. at 530: “Thus, unless Congress specifically has provided otherwise, courts traditionally have been reluctant to intrude upon the authority of the Executive in military and national security affairs.” Emphasis added.)
While regulation of this system has been effectuated through EOs, the last EO setting out parameters concerning the protection of national secrets, EO 13526, was issued by then-President Obama in 2009. President Trump never issued an EO concerning classification, and although the Biden administration has conducted a policy review and planned to release a new classification EO, this effort was delayed following the developments of the past year.
Congress’s role in the classification system over the past several decades has primarily involved issuing recommendations and orders to the executive branch to conduct declassification review of material concerning specific matters of public interest. After years of advocating for the declassification and release of 28 pages that were redacted from the 9/11 Joint Congressional Inquiry, HPSCI members Rep. Stephen Lynch (D-Mass.) and Rep. Walter Jones (R-N.C.) in 2013 introduced a resolution calling for the president to declassify the chapter, and in June 2016 the members introduced H.Res.779, which urged the HPSCI to publish the material in the Congressional Record, referring specifically to “the Constitution’s separation of powers and the congressional prerogative of disclosure under the speech or debate clause.” The Obama administration ultimately declassified the document the next month, which HPSCI published immediately.
Congress has also passed legislation to push for the release of classified material, such as the President John F. Kennedy Assassination Records Collection Act of 1992, which established an independent executive agency to collect, review, and declassify records concerning the Kennedy assassination. Similarly, a proposal in the NDAA would require the National Archives to collect records related to unidentified anomalous phenomena (also known as UFOs) and provides for a newly established board to review and disclose this material to the public. But this process of congressional orders for declassification still relies on federal agencies to approve declassification and disclosure, which has given rise to tension between the branches. In March of this year, for example, President Biden signed into law a bill introduced by Sens. Josh Hawley (R-Mo.) and Mike Braun (R-Ind.) ordering Director Haines to declassify and release “any and all information” related to “potential links between the Wuhan Institute of Virology and the origin of [the novel coronavirus].” In June, the senators accused Haines of failing to comply with the law by releasing an allegedly “incomplete report” past the statutory deadline.
Although Congress has some authority to disclose to the public classified information through votes taken by the SSCI and the HPSCI, the procedures outlined in the committees’ respective rules provide for executive input when the information slated for disclosure had been submitted to Congress by the executive branch and when the executive requests that the material be kept secret. Both chambers require the president to be notified of a committee vote to disclose this material and allow the president five days to consider whether the risks associated with the release of the information outweigh the public interest in disclosure. If the president determines that they do, the president may object to disclosure in writing and send the matter back to the appropriate chamber and committee for reconsideration. Congress and the White House may negotiate to redact certain information, as they did to release the executive summary of the SSCI’s study of the CIA’s Detention and Interrogation Program in 2014.
The plain text of the rules, however, suggests that the full Senate or House could theoretically vote to disclose material over presidential opposition, but this has never occurred and the constitutionality of this interpretive wrinkle is disputed. Moreover, the text of Section 8 of S.Res. 400 and Clause 11(g)(1) of House Rule X imply that these legislative bodies have limited authority over classified material—both refer to their ability to disclose, but not to declassify, classified information. This distinction may be of limited practical effect, but it could be legally important—congressional release of information that is still classified may give rise to liability under the Espionage Act, assuming the circumstances of disclosure do not fall within the scope of the Speech or Debate Clause.
These constitutional dynamics were brought to the fore in 2018 following the declassification and release of a memorandum of the HPSCI majority staff concerning the electronic surveillance of Carter Page. In a letter declassifying and releasing the document, then-White House senior counsel Don McGahn noted that the HPSCI’s request to release the memorandum was “interpreted as a request for declassification pursuant to the President’s authority” and explained that unilateral release of classified information by the legislative branch “is extremely rare and raises significant separation of powers concerns.” Following the memorandum’s release, the HPSCI took a second vote to disclose a rebuttal memorandum from HPSCI minority staff. In response to what was again interpreted as a “request for declassification,” the White House issued a letter indicating that the president is “unable to” declassify the rebuttal memorandum due to national security and law enforcement concerns. The letter noted, however, that the president was “inclined to declassify” the document, and it directed Justice Department personnel to be available to assist the HPSCI with revisions to the document “given the public interest in transparency in these unprecedented circumstances.” HPSCI minority members ultimately coordinated with the Justice Department and FBI to redact and release the rebuttal memorandum. While this constitutional question was never resolved, it provided an opportunity for scholars to consider whether Congress has unilateral authority to release classified information, despite executive branch representations that it does not.
Congressional involvement in setting classification standards therefore marks a seismic change not only in how national security information is regulated but also in who sets the regulations. Although executive orders allow successive presidential administrations to change classification standards without the delays attendant in the legislative process, the incorporation of classification and declassification standards and procedures in the proposed legislation is Congress’s way of declaring to the American people, and to the executive branch, that classification is a matter of the public interest as well. Particularly in the context of the reauthorization of Section 702 of the Foreign Intelligence Surveillance Act, the proposals contained in the bills offer opportunities for the government to balance the need for some intelligence activities to remain protected, while facilitating the removal of the veil of secrecy from material that the public has a legal, and perhaps even a constitutional, right to access.
Senate Proposals
For starters, and perhaps because of the U.S.’s constitutional separation of powers and system of checks and balances, many of the reforms contained in the proposed legislation introduced in the Senate in May (referred here as the Warner or Cornyn bills) concern requirements that have already been articulated in executive orders and agency guidance documents. This includes, for example, codifying original classification authority and training for such authority.
Other proposals envision more meaningful structural developments. The Warner bill appoints the DNI as the new “Executive Agent for Classification and Declassification” who will receive direction, advice, and guidance from, and must consult with, a newly established “Executive Committee on Classification and Declassification Programs and Technology.” Both bills enhance the role of the Public Interest Declassification Board (PIDB), an expert committee that has advised and provided recommendations to the president and other executive branch officials on the classification and declassification of national security information since 2000, including, in the Cornyn bill, by allowing the organization to hire staff members, relieving administrative and logistical burdens currently shouldered by the Information Security Oversight Office (ISOO).
The proposals also appear to address recent high-profile incidents of allegedly mishandled documents. The Warner bill codifies a requirement that each federal agency with access to classified information develop an insider threat program with minimum standards to better safeguard classified information and report to Congress annually on their compliance with the program. While presumably intended to address concerns surrounding the Discord disclosure, the requirements in many ways reflect the existing obligations of executive agencies and departments contained in Executive Order 13587, which was issued in 2011 following the disclosure of hundreds of thousands of classified documents by Army intelligence analyst Chelsea Manning to WikiLeaks. For its part, the Cornyn bill directs the director of ISOO, the DNI, and the PIDB to review studies and reviews conducted by federal agencies to assess and justify the number of personnel eligible for information across all clearance levels and special access programs (calculated to be in the millions), which may help limit the pool of potential wrongdoers, ease the identification of individuals who mishandle classified records, and reduce the overall cost of clearing and re-clearing personnel, a process that totaled over $1.5 billion across 39 agencies in fiscal year 2021.
Proposed safeguards around the documents of presidential officeholders in the Warner bill treat commingled or uncategorized records of the president and the vice President as presumptively “presidential records” and require that commingled or uncategorized records designated as “personal records” during their term in office undergo a security review by the archivist of the National Archives and Records Administration. If a president, vice president, or other agency head engages in the mishandling or the unauthorized disclosure of classified information, the director of the National Counterintelligence and Security Center must prepare a written counterintelligence assessment to Congress within 90 days of detection addressing the national security risk resulting from such conduct.
The Warner bill also codifies a balancing test for agencies to employ when initially classifying information, under which an agency can classify information only if the harm to national security that would result from disclosure outweighs the public interest in disclosure of that information. The proposal includes a presumption of nonclassification and declassification of information that had previously been classified where there is significant doubt whether national security interests outweigh the public interest in disclosure. To assist with the practical application of this balancing test, specific criteria are built into the Warner proposal. The national security concerns on one side of this scale include nine scenarios that largely track the nine situations articulated in Section 3.3(b) of EO 13526, in which an agency head may exempt information from automatic declassification, such as where disclosure of information would impair U.S. cryptologic systems or activities, or where disclosure would reveal information that would impair current national security emergency preparedness plans. On the other side of the scale are five factors related to the public interest in disclosure of classified information, specifically, whether disclosure of the information would (a) better enable citizens to hold government officials accountable, (b) assist the criminal justice system in holding persons responsible for criminal or extraconstitutional acts, (c) assist Congress in its oversight responsibilities vis-a-vis the executive, (d) assist with understanding the interpretation of a provision of law, or (e) bring about any other significant benefit, including an increase in public awareness or understanding of government activities or an enhancement of government efficiency. While these factors do not currently appear in any existing law or executive order, this same public interest language was included in the Government Secrecy Reform Act of 1998 (S.712), which failed to garner sufficient Senate support at the time and which the White House vigorously opposed on the basis that the balancing test could give rise to judicial review of classification and declassification decisions, threatening “essential Presidential authority.”
Finally, to manage the massive volume of documents that require declassification review, both proposals call for research into a technology-based solution to support efficient and effective systems for classification and declassification. Experts agree that while technology is in part responsible for the explosion of classified material, it also holds the solution for efficient declassification of this same information. To fund this solution, the Warner bill would create a “Declassification Working Capital Fund” in each agency with original classification authority, funded through financial transfers calculated based on a ratio of the number of classified records an agency subcomponent generates each year against other subcomponents—in essence, a “tax” to create a financial incentive for more conservative classification and to penalize an agency subcomponent for reflexive, sloppy, or irresponsible classification. The proceeds from these funds are dedicated to promoting and implementing technological and automated solutions for declassification. Although this proposal creates a concrete disincentive for overclassification that is absent from the current system, in practice it may be difficult to justify a greater financial burden borne by government divisions that have more acute classification needs.
While the bills reflect the ambitious aims of some of the most vocal advocates for classification reform in Congress, the classification proposals contained in the Senate’s July NDAA and in the classification bill introduced in the House in October significantly pare back the proposals, including reforms that appeared to be specific responses to recent events involving classified information. The NDAA and House proposals cut the oversight of a new executive agent and committee dedicated to classification and declassification, remove the codification of insider threat programs, eliminate the procedures concerning presidential and personal records, do away with the presumption of nonclassification and limit the public interest factors to the determination of records for declassification, and strike the funding mechanism to research a technology-based solution. The version of the NDAA released by House and Senate negotiators on Dec. 6, and which is likely to become law, scales back the proposals even further, leaving more modest commitments surrounding declassification review, training for agency employees to promote sensible classification, staff for the PIDB, agency studies on the necessity of security clearances, and research and implementation of a technology-based solution for classification and declassification.
The Need for Reform
No matter who has final authority over reform of the classification system, the scale of the problem is astonishing. Based on a 2017 ISOO report, nearly 50 million classification decisions are made each year, and the cost of maintaining the classification system is estimated at more than $18 billion annually. The current system for declassification faces significant backlogs, and this task is about to become exponentially more daunting as the queue of documents reaching their 25-year date for declassification review is reaching documents classified in the late 1990s—at the advent of the era of the digitization (and proliferation) of classified information. While these proposed reforms do not offer an immediate fix to the overwhelming job of declassification, and they cannot alone prevent the criminal mishandling or disclosure of classified information, they demonstrate Congress’s strongest attempt in years to play a role in the regulation and oversight of the classification system. The recent instances of allegedly mishandled documents highlight deficiencies in the U.S. government’s ability to protect classified material that can have serious national security consequences.
These concerns are also rooted in democratic principles—ineffective and inefficient declassification of material that is no longer sensitive infringes on government transparency and impedes accountability. Information disclosure from national institutions is even more crucial now to combat disinformation and thwart conspiracy theories that fuel extreme anti-government views. In ISOO’s 2022 annual report to the president, former ISOO President Mark Bradley aptly summed up the imperative that the U.S. government act to address this issue: “[S]o much remains to be done to rethink and to recast the ways we classify and declassify national security information. If we don’t change how we do both, our enemies will have an easier time stealing our secrets and many of our citizens will continue to not believe what their government is telling them.” By proposing reforms to the legal scheme of the classification system—and however modest those changes may ultimately be—Congress is asserting the public’s interest in a more effective, secure, and transparent structure to protect national secrets.



.jpg?sfvrsn=1111cf9d_6)

