Cyberspace is the New Battlespace
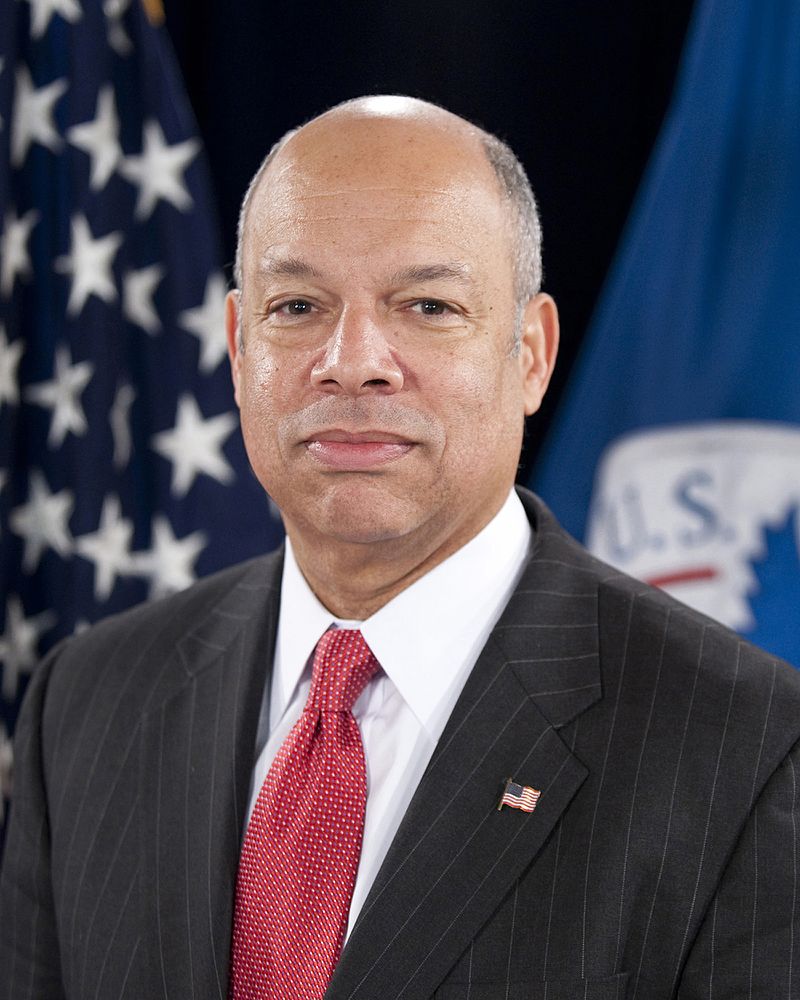
Editor's Note: This post contains the text of a speech that former Secretary of Homeland Security Jeh Johnson is delivering this hour at the Boston Conference on Cybersecurity.
***
Editor's Note: This post contains the text of a speech that former Secretary of Homeland Security Jeh Johnson is delivering this hour at the Boston Conference on Cybersecurity.
***
Given my prior experience at the Defense Department, I came to the Department of Homeland Security with a counterterrorism orientation. I said many times that counterterrorism is the reason DHS was created, and it had to remain the cornerstone of the Department’s mission. I quickly came to realize that a building can have more than one cornerstone, and that cybersecurity must constitute another.
Cyberattacks on and within our nation occur daily, hourly, and by the minute. Scores of them have occurred since I walked into this building a few minutes ago. No one is immune. The cyber threat to our nation is going to get worse before it gets better.
Bad cyber actors, ranging from nation-states, cybercriminals, hacktivists and those who engage in the growing Ransomware industry—are increasingly aggressive, ingenious, and tenacious. Those of us on defense struggle to keep up.
Cyberspace is the new battlespace.
History will record that the Obama administration, at the personal insistence of the president, made tangible improvements to our nation’s and the U.S. government’s cybersecurity. At DHS, we established automated real-time information sharing with the private sector, and deployed the new EINSTEIN 3A system across all civilian agencies of the U.S. government. President Obama issued Presidential Policy Directive 41, clarifying the roles of the various federal agencies in cybersecurity. In September 2015, we secured from the Chinese government its agreement to abstain from cyber-enabled theft of trade secrets for competitive advantage—an agreement that experts say the Chinese appear to have largely adhered to. We worked with Congress to enact the Cybersecurity Act of 2015.
But there is much more to do.
In 2012, my former boss, Secretary of Defense Leon Panetta, gave a speech at the Intrepid Sea, Air & Space Museum in New York City in which he predicted a “cyber Pearl Harbor.” At the time, I thought Leon was being a little overly dramatic in his language. Now, six years later, I realize Leon could have been right.
In 2016, the Russian government, at the personal direction of its President Vladimir Putin, orchestrated a series of cyberattacks on our Nation for the purpose of influencing our election that year.
We were attacked by the Russians, plain and simple.
The Obama administration took a number of steps to counter those attacks, based upon what we knew at the time. They included:
-
a direct and personal warning by President Obama to President Putin;
-
at least five public statements by me to state and local election officials warning them about the cyber threat to election infrastructure;
-
cybersecurity assistance to 33 states and 36 city and county election officials in the run-up to the 2016 election;
-
a joint statement by me and the director of national intelligence publicly accusing the Russian government of cyber thefts and disclosures intended to interfere with the U.S. election process;
-
a declaration by me on January 6, 2017 that election infrastructure in this country should be considered critical infrastructure; and
-
sanctions announced by the president on December 29, 2016 directed at two Russian intelligence services, four Russian intelligence officers and three companies that were involved in cyberattacks on our country, and the expulsion from our country of 35 Russian government officials.
The good news is that, so far as we know, no ballots were altered nor any votes suppressed in 2016 as a result of the Russian government’s cyberattacks.
But, plainly, the steps we took in the prior administration have not been enough to deter Russian attempts to influence our democracy.
How do we know this?
Last month U.S. intelligence chiefs warned us that the United States remains “under attack,” and that “persistent and disruptive cyber operations” by the Russians will continue “using election opportunities to undermine our democracy.”
In the face of this testimony, the American people have a right to know from our leaders: What are you doing about it?
One form of response is obvious.
All nation-states have certain behavior traits in common.
Whether a democracy, a monarchy, a dictatorship, or a communist regime, all nation-states respond to deterrents, and will abstain from behavior they know is cost-prohibitive. The Russian government, like any other nation-state, will respond to a sufficient deterrent.
It is now the responsibility of the current administration to follow through on those sanctions we announced in December 2016 and do even more.
On the prevention side, there are steps we can take as a nation to harden our defenses against cyberattacks generally, and the Russian government specifically.
Here, it’s important to place the threats to our democracy into three buckets.
First, the hacking and unwanted exfiltration and theft of data. There are the standard cybersecurity measures we must all pursue. Investments in better technology, public-private information sharing, and greater awareness by those who use our systems about the evils of phishing and spear phishing, are the basic answers.
Second, in 2016, we had a wake-up call, and certain vulnerabilities to our election infrastructure were exposed. Building on my designation of election infrastructure as critical infrastructure in January 2017, the current Department of Homeland Security, through the leadership of Assistant Secretary Jeanette Manfra, is taking serious steps to work with state and local election officials to strengthen their cybersecurity.
State election officials seem to be answering the wake-up call and are energized.
Given the electoral college and the nature of our politics, in which national elections can be decided in a few key precincts in a few swing states, the results dance on the head of a pin. The writers of the TV series House of Cards have figured that out; so can many others.
For an excellent assessment on how states are doing with their election cybersecurity, I refer you to a comprehensive and objective 50-state survey issued last month by the Center for American Progress. CAP actually gave each state a grade. No state got an A; 10 states got a B; 23 states received a C; 13 states received a D; and five states received an F.
CAP also includes recommended best practices for the states, which include minimum cybersecurity standards for voter registration systems, post-election audits, and voting machine certification requirements.
There is a lot of work to do, and the 2018 midterm election season is now.
Third, and finally, is the problem that can be considered a form of cyberattack, but not exclusively so—it is the problem of fake news and hateful, extreme views published and republished on the internet, used as a weapon by foreign and domestic forces to seek to alter elections, sow discord, or alter public opinion generally.
The recent indictment of 13 Russian individuals by the Special Counsel highlights that this, too, was part of the Russian attack against us in 2016. And, it may be years before we understand the full extent this aspect of the Russian attack had on our democracy in 2016.
Of the three buckets of cyber threat I mention here today, this problem is the most pervasive, and the hardest to solve.
Like many of you, when I was growing up we had gatekeepers for news, whether it was the local newspaper, or on the national level, Cronkite, Huntley or Brinkley. Even when I was in law school, I did not fully accept that something happened until I heard Walter Cronkite tell me it happened on the CBS Evening News.
With the internet, the information marketplace has no gateways through which to send or receive so-called news. It’s an open platform, with no journalistic standards to limit entry. Any individual with a keyboard and access to the internet can capture the American public’s attention with real or fake news, which is then just as accessible by Google search as the New York Times.
And this is how an increasing number of Americans, with shorter attention spans, receive their news and form their opinions and political views.
Our strength as an open and free society has also become our vulnerability – a vulnerability that is being exploited by a range of domestic and foreign actors.
What do we do about this?
Whatever we do, we should not forget who we are as a nation.
Addressing the problem of fake news and extremist views is not a matter for the security agencies of our government. Foreign influence in federal elections is a matter for the federal election laws, and activities that violate criminal laws are a matter for law enforcement.
Beyond that, we must be extremely careful not to go down the road of empowering security agencies to regulate or restrict speech, particularly political speech, on the suspicion that it might have a foreign or extremist origin.
Imagine the dangers we would be tempting if we gave our political leaders the power to do this.
This is something they do in certain other countries; not here.
In my view self-regulation by private internet access providers is the best solution. And increased public skepticism about what we read and see.
This past weekend a pioneering journalist named Steven Brill, founder of the American lawyer magazine and Court TV, formally announced that he’s formed a new company called NewsGuard. It’s mission: reliability ratings for sources of on-line news, as determined by an independent team of journalists: green for trustworthy, yellow for consistently biased or inaccurate, or red for deliberately deceptive. Those that provide the platform for on-line news would need to incorporate the ratings into search results.
We face a threat to our very democracy. For, if voters cannot make informed and rationale choices about their leaders or their views on the issues, free of covert foreign influence, there is no true democracy.
In closing, I will repeat what I said numerous times in public office. Those that know history will learn from it; those that don’t know the mistakes of history are bound to repeat them.
Thank you.
***