Shadow Brokers Redux: Dump of NSA Tools Gets Even Worse
The Shadow Brokers are back. Back in August, the group released a large number of stolen tools purportedly hacked from “the Equation Group,” which is near-unanimously believed to be the NSA. In addition to the released files, Shadow Brokers announced an “auction” for the sale of an addition batch of NSA tools.
The Shadow Brokers are back. Back in August, the group released a large number of stolen tools purportedly hacked from “the Equation Group,” which is near-unanimously believed to be the NSA. In addition to the released files, Shadow Brokers announced an “auction” for the sale of an addition batch of NSA tools. At the time, it seemed the auction was more publicity stunt than money-making endeavor and that suspicion was confirmed last week, when they released the password for the auction tools for free.
The “auction” file materials were underwhelming, but today those wiley and sarcastic (and probably Russian) hackers dumped the really amazing stuff: operational notes from the NSA’s active targeting of banks in the Middle East and the NSA’s collection of Microsoft Windows exploitation tools. This may well be the most damaging dump against the NSA to date, and it is without question the most damaging post-Snowden release.
The operational notes on the NSA’s program extracting SWIFT data from Middle Eastern banks appear to date from September 2013, so this represents post-Snowden stolen data. The material is almost certainly legitimate—a spot check of data shows a large amount of consistency. This details exact targets, such as particular systems in eastnets.com to leverage access into the SWIFT systems of client banks, and sql queries designed to extract, in bulk, transactions of interest. Any access NSA maintained is now as good as eliminated, since this provides a detailed roadmap to how the NSA accessed this critical information.
The released may also cause substantial diplomatic fallout, as the U.S. government’s access to SWIFT has long been controversial.
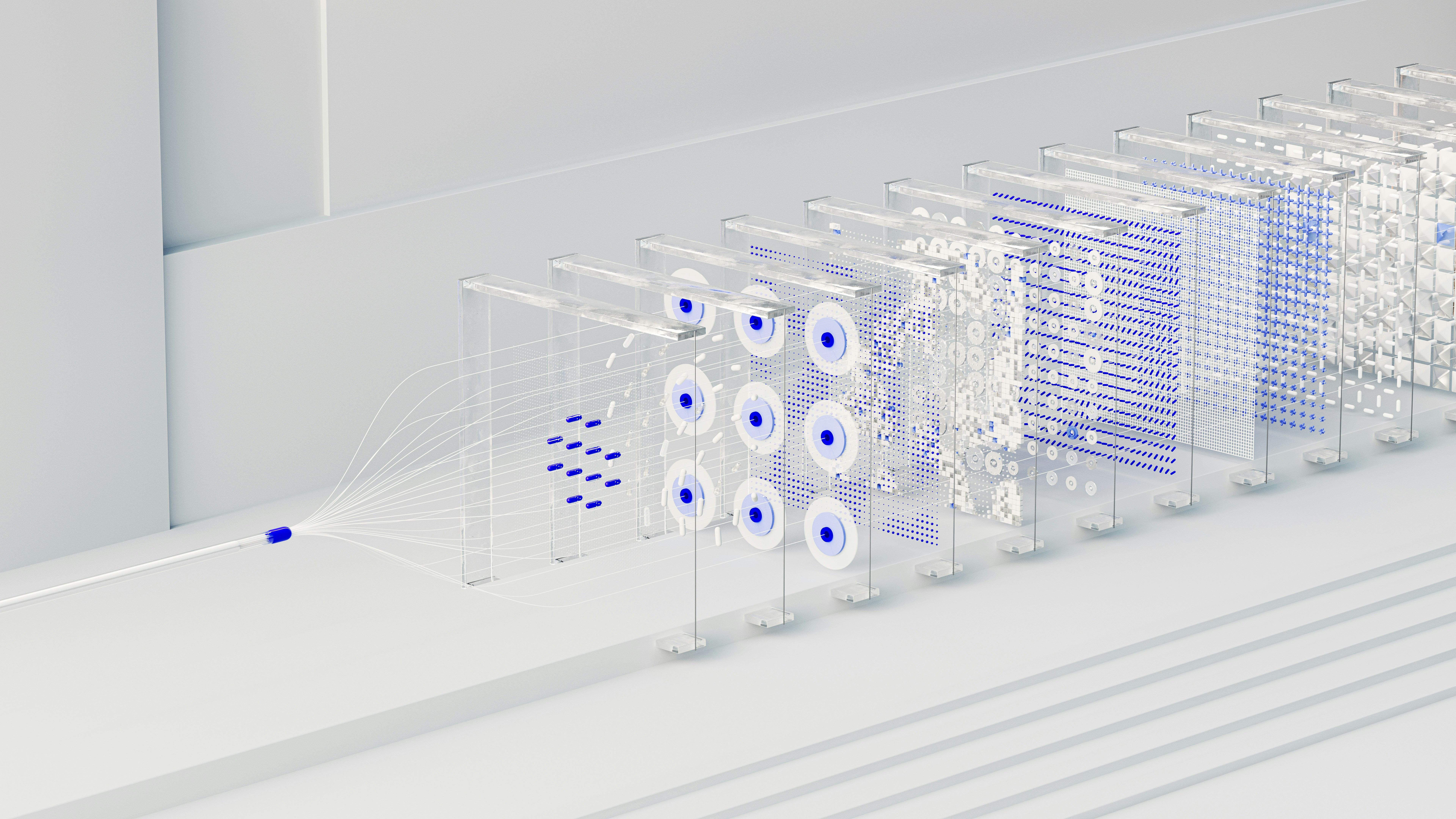
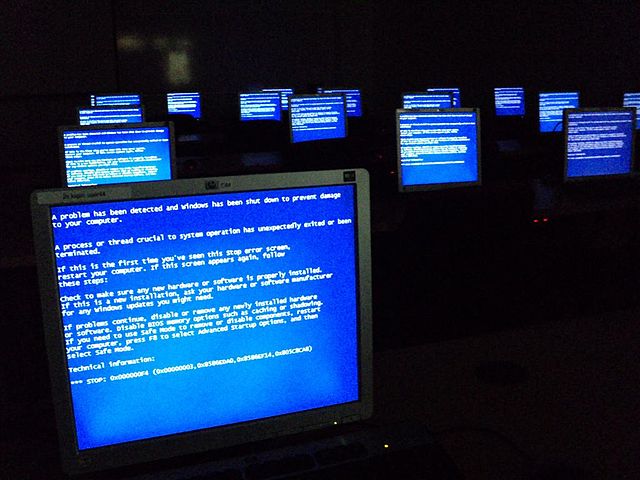
The technical damage, however, will likely exceed the political damage. The windows directory contains FuZZbuNch, which is effectively the NSA’s equivalent to the Metasploit toolkit: a easy-to-use framework for writing and launching exploits. Along with FuZZbuNch, the director contains multiple exploits. Preliminary analysis from Matthew Hickey, aka @hackerfantastic suggests that this framework not only works well but is integrated with multiple remote Windows exploits. These appear to have been stolen sometime in 2013 and were 0-days at the time targeting Windows 8 and Windows Server 2013. It is now confirmed that at least one 0-day still works against Windows Server 2013.
Normally, dumping these kinds of documents on a Friday would reduce their impact by limiting the news cycle. But Friday is the perfect day to dump tools if your goal is to cause maximum chaos; all the script kiddies are active over the weekend, while far too many defenders are offline and enjoying the Easter holiday. I’m only being somewhat glib in suggesting that the best security measure for a Windows computer might be to just turn it off for a few days.
This dump also provides significant ammunition for those concerned with the US government developing and keeping 0-day exploits. Like both previous Shadow Brokers dumps, this batch contains vulnerabilities that the NSA clearly did not disclose even after the tools were stolen. This means either that the NSA can’t determine which tools were stolen—a troubling possibility post-Snowden—or that the NSA was aware of the breach but failed to disclose to vendors despite knowing an adversary had access. I’m comfortable with the NSA keeping as many 0-days affecting U.S. systems as they want, so long as they are NOBUS (Nobody But Us). Once the NSA is aware an adversary knows of the vulnerabilities, the agency has an obligation to protect U.S. interests through disclosure.
The real mystery here is why the Shadow Brokers released this data. Ordinarily, a hostile intelligence service wouldn’t tip their hand by showing that they had obtained this information but there are some clear strategic benefits to that kind of signalling. Releasing the vulnerabilities themselves goes a step further. It ensures not only that the NSA is unable to use the Windows 0-days against targets, but that you aren’t either. It is a matter of short time before these tools are patched, and thus unavailable to anyone. These are tremendously valuable tools to just burn that way, so it does make one wonder (and worry): what exactly is the intended payoff here?
UPDATE: Further analysis suggests that at least one exploit will also successfully compromise Windows 10 without modification. It really is a good weekend to turn off your computer.
UPDATE II: Strike that previous update. Further reporting suggests that the mysteriously delayed Microsoft Patch Tuesday actually included patches for these tools, which suggests that the NSA did notify Microsoft in January when the Shadow Brokers released a directory listing suggesting they had these tools. It's great to wake up on a Saturday morning and find out you were wrong about things.