Steptoe Cyberlaw Podcast: ICCE Panel on Encryption and National Security
No holds are barred as a freewheeling panel of cryptographers and security pros duke it out with me and the Justice Department over going dark, exceptional access, and the Apple-FBI conflict.
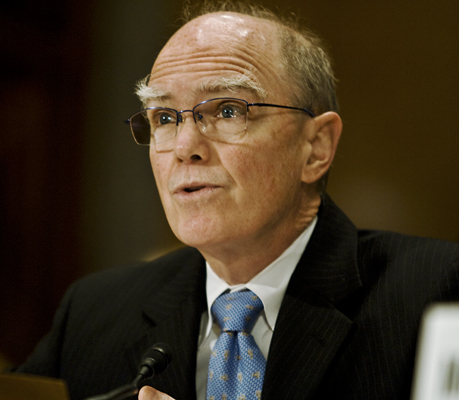
No holds are barred as a freewheeling panel of cryptographers and security pros duke it out with me and the Justice Department over going dark, exceptional access, and the Apple-FBI conflict. Among the combatants: Patrick Henry, a notable cryptographer with experience at GCHQ, NSA, and the private sector; Dan Kaminsky, the Chief Scientist at White Ops; Kiran Raj, who is Senior Counsel to the Deputy Attorney General; and Dr. Zulfikar Ramzan the CTO of RSA Security. Our thanks to Catherine Lotrionte who generously agreed to let me record this one-hour panel at her remarkable Annual International Conference on Cyber Engagement.
In the news roundup, Maury Shenk discusses the real and mythical import of the UK’s pending surveillance bill, and I mock the journalists who claimed to find scandal in GCHQ’s elaborate compliance regime for access to bulk personal data. Alan Cohn and I return to the Apple-FBI fight, and I can’t help pointing out that Apple, the self-proclaimed champion of security, didn’t bother to tell its customers that it was no longer providing security patches to QuickTime on Windows. Alan manages to explain Apple’s thinking with two words: “on Windows.”
The FBI’s decision to manage a child porn distribution node for a few weeks and prosecute its customers has come a cropper, but not for the reason you might think. Instead, Alan reports, at least one court is now willing to enforce the limits of Rule 41 and declare that a Virginia magistrate cannot issue a search warrant for a computer located in Massachusetts. That ups the stakes for the ongoing effort to amend this problem out of the Federal Rules.
I read an 80-page FISA opinion so you don’t have to. One of the technolibertarians’ favorite proposals – requiring warrants for searches of already-collected 702 data – has now been briefed to the court by one of the first FISA amici. And rejected. The argument was slapped down in an opinion by Judge Hogan. In the old days, government critics would have been able to press such an argument for years; now, thanks to the vigilant FISA amici and the transparency in FISA opinions that they cried for, that argument has suffered a body blow before it has even built up a head of steam.
And, just to show that we yield to no one in condemning abusive government data collection, I brief our listeners on where all the data created by their cheap Chinese drones is ending up – and which government has access to it. Suddenly, European-style data export bans are acquiring a strange new appeal.
As always, the Cyberlaw Podcast welcomes feedback. Send e-mail to CyberlawPodcast@steptoe.com or leave a message at +1 202 862 5785.
Download the 113th episode (mp3).
Subscribe to the Cyberlaw Podcast here. We are also now on iTunes, Pocket Casts, and Google Play!
The views expressed in this podcast are those of the speakers and do not reflect the opinions of the firm.