The Cyberlaw Podcast: Fighting Ransomware By Pushing All the Buttons on the Dashboard
The Biden administration’s effort to counter ransomware may not be especially creative, but it is comprehensive. The administration is pushing all the standard buttons on the interagency dashboard, including the usual high-level task force and a $10 million reward program (but not including hackback authority for victims, despite headlines suggesting otherwise). And all the noise seems to be having some effect, as the RE ransomware gang's web sites have mysteriously shut down.
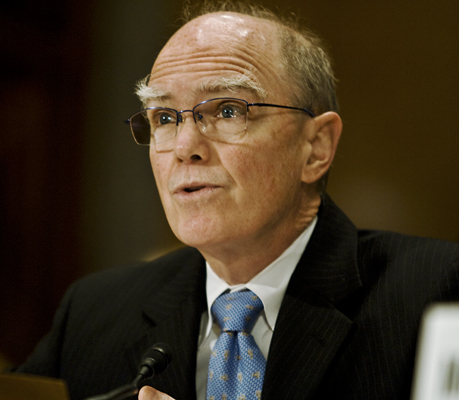
Our interview is with Josh Steinman, who served as the National Security Council’s Cybersecurity Senior Director for the entire Trump administration. He offers his perspective on the issues and the personalities that drove cybersecurity policy in those chaotic years. As a bonus, Josh and I dig into his public effort to find a suitable startup, an effort we have to cut short as I start getting too close to one of the more promising possibilities.
Nick Weaver reminds us (in song, no less) that the government’s efforts to stop scourges like Trickbot have a distinct whiff of Whack-a-Mole, and the same may be true of REvil.
Maury Shenk covers the Biden administration’s belated but well-coordinated international response to China’s irresponsible Microsoft Exchange hack, including the surprising revelation that China may be back to hacking like it’s 1999—relying on criminal hackers to serve the government’s ends.
In other China news, Maury Shenk and Pete Jeydel catalog the many ways that the current regime is demonstrating its determination to bring China’s tech sector to heel. It’s punishing Didi in particular for doing a U.S. IPO despite go-slow signals from Beijing. It’s imposing cybersecurity reviews on other companies that IPO outside China. And it seems to be pressing for competition concessions that the big tech companies would have successfully resisted a few years ago.
It was a big week for state-sponsored attacks on secure communications. Nick and I dig in the FBI and Australian federal police coup in selling ANOM phones to criminal gangs. Previewing an article for Lawfare, I argue that the Australian police may have to answer tough questions about whether their legal authority for the phone’s architecture really avoided introducing a systemic weakness into the phone’s security.
Law enforcement agencies around the world could face even tougher questions if they’ve been relying on NSO or Candiru, Israeli firms that compromise mobile phones for governments. Both firms have been on the receiving end of harsh forensics analyses from Amnesty International and Citizen Lab. Nick thinks the highly specific and centralized target logs are particularly a problem for NSO’s claims that it doesn’t actually know the details of how its malware is deployed.
Pete Jeydel tells us that the administration is learning to walk and chew gum on cybersecurity at the same time. While coordinating pushes on Chinese and Russian hacks, it also managed to get big chunks of the government to turn in their federal cybersecurity homework on time. Pete talks us through one of those assignments, the NTIA’s paper setting minimum elements for a Software Bill of Materials.
It wouldn’t be the Cyberlaw Podcast without a brief rant on content moderation. The Surgeon General claimed this week that “Misinformation takes away our freedom to make informed decisions about our health.” He didn’t say that administration censorship would give us our freedom back, but that seems to be the administration’s confident view, as the President, no less, accuses Facebook of “killing people” by not jumping more quickly to toe the CDC’s official line.
And if you thought it would stop with social media, think again. The White House is complaining that telecom carriers also should be screening text messages that are hostile to vaccinations.
Finally, just to show that the world has truly turned upside down, Maury reminds me that a German—German!—court has fined American social media for too enthusiastically censoring a lockdown protest video.
Pete tells us what’s in the new Colorado privacy bill. Short version: it joins Virginia’s in some of hosing down California’s excesses.
And in short takes:
- Maury explains Vietnam's version of China’s fifty-cent army.
- Nick explains why Psiphon is a better tool for evading Cuban censorship that the sleaze-infested Tor system.
- Maury updates me on the European Parliament LIBE committee’s latest proposal for accepting the U.S. intelligence community’s transatlantic surrender on data flows.
- And Pete tells us that the Securities and Exchange Commission may finally be putting the screws to companies that have been lax about reporting breaches to their investors.
And more!
Download the 371st Episode (mp3)
You can subscribe to The Cyberlaw Podcast using iTunes, Google Play, Spotify, Pocket Casts, or our RSS feed. As always, The Cyberlaw Podcast is open to feedback. Be sure to engage with @stewartbaker on Twitter. Send your questions, comments, and suggestions for topics or interviewees to CyberlawPodcast@steptoe.com. Remember: If your suggested guest appears on the show, we will send you a highly coveted Cyberlaw Podcast mug!
The views expressed in this podcast are those of the speakers and do not reflect the opinions of their institutions, clients, friends, families, or pets