Data Security and U.S.-China Tech Entanglement
U.S. policymakers must have an accurate understanding of how Chinese government access to data works in order to respond to the risks posed in the most responsible and effective manner.
I stood at the witness table, my heart pounding, and raised my hand to take an oath. Sen. Josh Hawley had just berated Apple and TikTok for yet again declining his invitation to testify at the hearing. Flanked by their empty seats, I knew I was not going to be interrogated, but I also knew that what I had to say would not distill into sound bites that a crusading Hawley could use as props in his show.
That show built on Hawley’s declaration last fall that Apple and TikTok are “two sides of the same coin when it comes to data security: the danger of Chinese tech platforms’ entry into the U.S. market, and the danger of American tech companies’ operations in China.” He then introduced a draft bill that would prohibit companies from storing and transferring U.S. citizen data to countries of concern (identified as China, Russia or any country designated as such by the secretary of state).
There are data security risks posed by U.S.-China technology entanglement. As Hawley and others routinely say: Ultimately the Chinese government can compel companies to turn over their data. But this does not always happen. Compliance with Chinese law is a negotiation and is never black and white. Yet, if U.S. policymakers conclude that they cannot guarantee the protection of the data in China, why is it even important to understand that there is an internal push and pull, driven by different stakeholders with often-conflicting agendas?
U.S. policymakers must have an accurate understanding of China’s cyber governance system and Chinese government access to data in order to respond to the risks posed in the most responsible and effective manner. In this post, which is based on the testimony I submitted for the hearing chaired by Hawley and Ranking Member Sen. Sheldon Whitehouse on March 4, I offer recommendations for how to do this:
- U.S. policymakers should start with an accurate understanding of the complexities of cyber governance in China. Doing so also means differentiating the risks associated with Apple and TikTok because different kinds of risk require distinct policy responses.
- The U.S. government should put in place more robust rules for data access and retention for all companies regardless of national origin.
- Given the rise in data sovereignty around the world, U.S. lawmakers should be careful not to create a blueprint for countries (such as India) to block data flows to the United States since access to large, international datasets is vital for U.S. competitiveness in artificial intelligence (AI).
China’s Cyber Governance System and Chinese Government Access to Data
U.S. policymakers need to start with an accurate understanding of the nature of the risks posed by China’s cyber governance system.
First, U.S. policymakers should not conflate the problems of (a) U.S. companies operating inside China with (b) Chinese companies operating in the United States. Different policy approaches are required to address two separate sets of risks. The first is U.S. companies like Apple operating in China (handling mainly Chinese citizen data) and the second is Chinese companies like TikTok operating in the United States (handling mainly U.S. citizen data). Because U.S. firms in China manage mostly Chinese citizen data, this poses serious ethical and market-access questions. This concern is distinct from the national security question of Chinese companies having access to massive amounts of U.S. citizen data overseas.
The data handled by U.S. firms operating in China is primarily Chinese citizen data, and in some cases, China segments its global networks to prevent Chinese citizen data from flowing outside of China, in accordance with Chinese law. The challenges for U.S. firms in this context are ethical: How will they respond to pressure from the Chinese government to turn over the content of user emails or search histories to crack down on dissent? Do these firms have control over and visibility into supply chains to prevent the company’s technology from enabling the Chinese government to commit mass human rights violations today or in the future? The mass incarceration of minorities in areas like Xinjiang or Tibet is just one example. A new report by the Australian Strategic Policy Institute describes Uighurs in prison-like forced labor conditions at Chinese factories reported to supply U.S. companies such as Nike.
In my previous congressional testimony, I argued for the development of new legislation and standards to systematically consider the ethics of specific partnerships in China. This is too big and complex a challenge for individual companies to take on themselves. Existing voluntary guidelines like the Global Network Initiative (GNI) are not up to the task of addressing the problem. But neither of the two extreme positions I often hear—pretending these issues do not exist at all, or pushing to sever all research and commercial ties with China—serve U.S. interests and values.
U.S. firms also face market-access barriers and costs due to Chinese government restrictions on the cross-border transfer of data. Article 37 of China’s Cybersecurity Law requires that certain kinds of data (“important data” and “personal data”) must be stored on local servers or undergo a security assessment before being sent outside of China. There still appears to be a regulatory gray zone in which multinationals in China can send certain kinds of data outside the country, but the extent to which this will be the case in the future is unclear, given the significant weight that national security has in Beijing’s approach to data regulation.
This is a separate question from the other key issue: The way Chinese companies handle U.S. citizen data does impact U.S. national security. This could mean a Chinese app collecting data from overseas users, like TikTok, or a Chinese company seeking to acquire a U.S. company that has data collected on Americas, like the Ant Financial/MoneyGram deal blocked by the Committee on Foreign Investment in the United States (CFIUS).
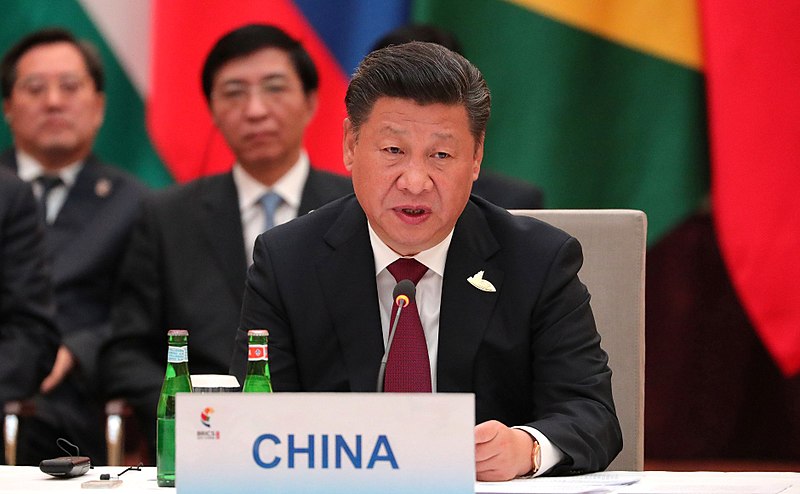
This brings me to my second point: The Chinese government does not necessarily have unfettered real-time access to all companies’ data. Chinese President Xi Jinping’s government has built the world’s most comprehensive cyber governance framework. With the 2017 Cybersecurity Law as the centerpiece, a sprawling framework governs data security and transfer, critical infrastructure, and digital content. This framework underpins the world’s most sophisticated system for online control, which the Chinese government has used to monitor and restrict population movement to control the spread of the novel coronavirus. And on March 1, a new sweeping regulation for censoring content took effect.
U.S. and Chinese firms must comply with these requirements to operate in China. But what exactly does compliance mean in practice? Nothing is black and white, particularly when it comes to government access to data. Ultimately the Chinese government can compel companies to turn over their data, but this does not always happen.
U.S. policymakers must start with a fact-based understanding of the reality on the ground, taking into account the internal push and pull of different actors in the system, and the gray zones in the rules. Chinese corporate actors are not synonymous with the Chinese government or the Chinese Communist Party; these actors have their own commercial interests to protect. Failure to take into account the friction within the system can lead to dangerous policy outcomes; decoupling and conflict with China are not in the interest of U.S. security or economic prosperity.
Companies Push Back on Data Requests
Many Chinese companies will discuss privately that they routinely push back against data requests from the government, but they do not want to talk publicly about that because doing so draws attention to themselves. In fact, drawing attention to themselves would be counterproductive to the ultimate goal of fighting against government intrusion. In China, media attention will only lead government officials to double down on their request.
A few examples have come out publicly. The Chinese ride-sharing company Didi initially refused to turn over data to law enforcement authorities investigating the murder of passengers. Tencent and Alibaba refused to feed their transaction data to a government credit reporting program under the People’s Bank of China. The Chinese app WeChat states that it does not store the content of user chats for data mining, which may be driven in part by a desire to avoid entanglement with the government, according to an article in the Harvard Business Review.
It is also important to keep in mind that data requests are made in a manual fashion: The government makes a request, and then the company reviews that request and responds. Moreover, there is no single government repository of all data. The People’s Bank of China and the National Development and Reform Commission, the state agency responsible for state economic planning, have a history of not sharing data with each other. This is not surprising given the tremendous political power that certain kinds of data can yield in the Chinese system.
China’s Cyber Regulatory Regime and Data Access
I’d like to walk through how the regulatory regime related to government access to data in China works since the system is very difficult for outsiders to understand in English, let alone by reading the original directives in Chinese. Moreover, many commentators in the U.S. have no experience with the process involved for companies undergoing cybersecurity-related audits in China.
Among the concerning parts of this cyber governance framework, the Cybersecurity Law (Article 28) states that “[n]etwork operators shall provide technical support and assistance to public security organs and national security organs that are safeguarding national security and investigating criminal activities in accordance with the law.” This vague language (which is echoed in the 2015 Counterterrorism Law and National Security Law) does provide an opening for the government to compel companies to collaborate with intelligence services and law enforcement. Does “technical support” mean turning over encryption keys? Does it mean data monitoring by the security services? Maybe, maybe not.
Compliance often involves lengthy and complicated negotiations between companies and local officials. Local officials must balance competing demands of security with immense pressure to deliver economic development in their jurisdiction. The Chinese Communist Party derives its ruling authority in large part by providing economic prosperity. Furthermore, different local government agencies often have different objectives. Sometimes companies will leverage connections with officials from other agencies to stop security bureau officials from seeking certain kinds of data. These factors create a kind of backstop on how far the government tends to go in implementing some of the most worrisome provisions of China’s cyber governance regime.
There are two recent developments in China’s cyber governance system in which risk of data access is at issue: a regulatory scheme called the Multi-Level Protection Scheme (MLPS) and the Cryptography Law. Both apply to Chinese and U.S. firms in China.
Multi-Level Protection Scheme 2.0 (MLPS 2.0). MLPS is a security certification regime that the Chinese government established in 2007. In 2018, China’s Ministry of Public Security released a draft of a new version (referred to as MLPS 2.0). The draft regulation updates the original MLPS regime based on the new principles set out in the 2017 Cybersecurity Law. MLPS ranks from 1 to 5 all information and communications technology systems based on their importance to national security, with Level 5 deemed the most sensitive. Anything ranked Level 3 or higher triggers a suite of regulatory requirements. Companies initiate the process by conducting a self-assessment and working with a third-party auditor (typically linked with the local public security bureaus); the auditor conducts interviews on-site and observes testing and verification performed by the company. The auditor then writes a report for the provincial or city-level public security bureau.
To be sure, MLPS 2.0 creates more regulatory scrutiny on foreign technology, along with a host of new market-access barriers as the Xi government doubles down on reducing reliance on foreign suppliers and boosting indigenous equipment. While the 2007 version of MLPS targets only information systems controlled by the government, the updated regime covers all information systems (all “network operators”), meaning that all private and foreign companies now fall under the scope of the review. In the current environment, MLPS 2.0 also appears to have a focus on cloud computing, big data platforms and the “internet of things.”
While the updated regime creates a monumental regulatory headache, there is nothing written down under MLPS that requires firms to provide access to all of their data (or provide encryption keys to the Chinese government). There is a provision that requires information systems graded Level 3 and higher to undergo “cybersecurity monitoring” connected to the public security agency. But there is no definition of what exactly this entails—Does this mean a sleepy security guard sits in a facility, or a device is installed in the network? The audit is a negotiation—a give and take in which companies hash out with regulators a way to be compliant but not go as far as the most conservative interpretation of the requirements. Again, local bureaus responsible for economic growth in their jurisdictions do not have incentives to demand that companies turn over all of their data. Chinese government regulators understand that certain MLPS requirements such as the use of Chinese domestic encryption (as discussed in the next section) create tremendous costs and challenges for foreign companies, which means the use of domestic encryption by foreign firms is rarely enforced.
The final regulation for MLPS 2.0 has not yet been released. The latest development in late 2019 is that the core standard of MLPS took effect (spelling out the requirements for each of the five levels of the graded system).
New Cryptography Law. The two most important things to understand about China’s encryption regime are that (a) the Chinese government wants all companies to use Chinese encryption algorithms and (b) the vast majority of foreign companies do not do this and regulators rarely enforce it.
The problem, however, is that it is unclear whether this will be the case in the future.
A major change is underway with the release of the Cryptography Law (which entered force Jan. 1). This law overhauled China’s encryption regime after two decades of intense internal debate. The law is concerning on several fronts, but it is too early to determine the impact it will have as additional regulations are forthcoming that will offer more details about the law’s scope and how it will be implemented for companies. (New regulations plus standards tied to those will eventually update a 1999 regulation called the Regulation on the Administration of Commercial Cipher Codes.)
This new law introduces two important changes, among other developments:
First, it eliminates a significant carve-out that has benefited foreign companies for years. Under the previous regime, centered on the 1999 Regulation on the Administration of Commercial Cipher Codes, the government granted what is known as the “core function exception.” This meant that the government permitted the use of products designed with encryption as a general feature (for example, commercial software). In contrast, products designed to be encryption or security products as their “core” function would face restriction. So companies like Symantec and encryption hardware manufacturers, for example, were excluded from the Chinese market, leaving domestic firms to dominate these business segments. However, for the past two decades, many companies have benefited from the carve-out, including server, database and software companies considered not to have encryption as their core function.
The new law is a potential game changer by removing this exception. It is still too early to know whether this means products allowed under the previous regime could be restricted or if they will still be allowed albeit with a new approval process. Nobody knows yet. In place of the exception, the government has indicated that it will focus on requiring certifications for the 15 products listed in the “Catalogue of Critical Network Equipment and Network Security-Specific Products.” This Catalogue, which includes items like routers, switches, and industrial manufacturing controllers, came out with the Cybersecurity Law in 2017 and lists network products that must receive a certification before they can enter the market. It is also possible that the new regime could create some new openings for foreign companies, especially smaller companies.
The second change is that the new law creates a separate category of what is called “commercial encryption” (distinct from “core” and “common encryption,” both of which apply to state secrets, “core” being the most sensitive). Any item that is identified as commercial encryption for use in a “mass consumption product” will not be subject to an import license. The government has not yet released regulations to clarify the scope of “mass consumption,” again creating much uncertainty. Depending on how the law is implemented, this could mean lifting the burden of having to navigate a lengthy administrative review process (which is often subject to bribery).
Is operating in a regulatory gray zone—one in which the government has all the power and can change course at any moment—a wise decision for a U.S. company? That is not my area of expertise. I highlight these ambiguities so that U.S. policymakers have an accurate picture of how the process works.
Recommendations
China poses real cyber risks to the United States spanning ethical, commercial and national security. If the Chinese government wants something, they can get it, so why is it even important to understand the nuance of how the process works in China, and the fact that there is a thriving debate on data access among different players? Only with an accurate understanding of China’s system can U.S. policymakers develop an effective response that secures data while maintaining U.S. leadership in emerging, data-intensive technologies.
Build More Robust Rules for How All Companies Access and Retain Data
To address the risks presented by Beijing, the United States should not be reactive but, instead, actively seek to set out a different vision for U.S. internet governance based on a rule-of-law system.
In China there is no guarantee that the government cannot access data because China’s system lacks clarity of law, oversight mechanisms and clear pathways for contestation. As the United States looks to strengthen its own data privacy and cybersecurity system, there are important lessons policymakers can learn. Establishing clear authorities and oversight capacity enables the U.S. government to conduct legitimate national security and law enforcement investigations in such a way that upholds civil liberties and is subject to review and appeal. Here the United States has an opportunity to set out a different vision for U.S. internet governance, one that strikes the appropriate balances among national security, economic and privacy concerns in a way that promotes strong democratic norms and protects data flow openness.
The United States would be wise to spend more time working on legislation and the development of standards to better protect privacy and secure data—not just in dealing with China, but for all companies. Lawmakers should accelerate progress on a number of bills addressing algorithmic transparency, strengthening cybersecurity and mandating higher standards for personal data. Developing a comprehensive federal privacy bill is vital to this effort, along with the creation of strong enforcement mechanisms. Inaction by the United States means ceding leadership and influence to both Europe and China in setting international standards.
Moreover, without higher standards for data security and privacy, U.S. citizen data held by unregulated private companies will be more vulnerable to breaches by hackers from China. Equifax’s many security issues are well documented, such as the company’s failure to patch known vulnerabilities that ultimately left exposed the data of 145 million Americans. But the hack was also conducted by a foreign government entity with sophisticated hacking capabilities and access to considerable state resources. Setting minimum standards on what data can be collected and retained by all companies will help protect U.S. personal data, regardless of whether the risk is exacerbated by a state-sponsored hacker, a data broker or a private company transferring the data to Beijing. Companies should not even have access in the first place to so much personal data that can be hacked or transmitted back to Beijing.
Address Cyber Risk From China in a Way That Avoids a Race to the Bottom in ‘Data Hoarding’
U.S. actions to respond to data security risks posed by the Chinese government are not occurring in a vacuum. The United States’s policy approach should be tailored to take into account the fact that technology competition with China will play out not only in the United States and China but also in other places, from India to Europe. How the U.S. government responds to Chinese companies operating in the United States will have ramifications for whether other countries are willing to accept our vision of data governance.
The ability of U.S. firms to maintain a high rate of innovation depends on access to global markets; talent; and, perhaps most important, datasets. But an increasing obstacle to the ability of U.S. companies to operate internationally—beyond China—is rising data sovereignty elsewhere, from Europe to India to Vietnam. Some U.S. policymakers also refer to this as “data hoarding,” which means efforts by nation-states to ensure control over data by prohibiting transfers of data out of the country or by seeking to limit foreign access to certain kinds of data. In this context, our actions will serve as a reference and a road map for other governments that are concerned about U.S. companies and the U.S. government getting access to their data.
For example, Indian lawmakers are in the middle of debating a draft data protection bill that would require local storage and processing of Indian citizen data in an effort to boost local technology firms as well as push back against data collection by large U.S. companies. The U.S. government and U.S. industry have lobbied against this law. In this context, the United States’s establishing (or, arguably, contributing to) a precedent of strict data localization rules risks other countries following suit. According to a U.S. government official, Indian officials are citing Hawley’s proposal as justification for Indian data localization.
If U.S. firms cannot send data out of countries in which they operate overseas, they lose access to the value of being able to create international datasets. This directly impacts economic growth and AI innovation because of the ways large, diverse, international datasets are core to building AI applications that work across a variety of geographies, languages, cultures and demographics. A language translation system trained only in China, for instance, will likely not accurately and precisely capture all of the world’s spoken languages as much as a language translation system with data from many different countries. Skin cancer predictors trained only on lighter skin tones, to give another example, are likely to have poor accuracy and precision when trying to predict skin cancer with darker skin tones. Policies that leave companies without any access to global datasets under any circumstances will lead to a “fracturing” of how AI applications are developed.
The United States has an opportunity to set the standards for protecting the flow of data that has underpinned economic growth and the free flow of information around the world, but with the right safeguards in place.
The challenge, therefore, is how to maintain this openness but with the right guardrails in place. The first step is to limit companies’ access and retention of data across the board, as discussed earlier.
The U.S. also needs to take a targeted approach to restrictions on Chinese companies. In my previous testimony I argued for an approach based on the idea of a “small yard, high fence,” borrowing a phrase used by former Secretary of Defense Robert Gates that means being selective about what the U.S. protects, yet aggressive in protecting it. The same idea should apply to restrictions on access to U.S. citizen data.
The expanded powers of the CFIUS provides one tool to do this. The U.S. government should evaluate the risks when a foreign firm acquires or takes a noncontrolling investment stake in an American firm that holds U.S. citizen data. As Robert Williams writes, the CFIUS’s case-by-case approach to evaluating risk is best understood as a scalpel and not a sledge hammer.
Whether through the CFIUS or other policy tools, any new restrictions must take a risk-based approach. Not all data has the same level of sensitivity. The mere fact that a Chinese company handles U.S. citizen data in and of itself may not necessarily warrant banning a transaction or blacklisting a specific company. The U.S. national security risks should be evaluated based on an investigation, with regular audits, to determine (a) what kind of U.S. citizen data is being accessed (for example, metadata, images, geographic data, critical infrastructure data), (b) how that data is being used and what data protection measures are in place to protect the rights and interests of U.S. consumers, and (c) with whom that data is being shared and through what mechanisms. If, based on the outcomes of such an evaluation, the U.S. government cannot verify that the interests and rights of U.S. consumers will be protected, then that company should be prohibited from storing and sharing U.S. personal data.
Conclusion
In short, the U.S. government needs a more effective strategy to protect U.S. personal data than one-off bans on companies or where they send their data. The U.S. needs to address legitimate national security risks where they exist and also as one part of a broader U.S. initiative on comprehensive data privacy and higher standards for cybersecurity for all companies (whether U.S. or foreign). These efforts should not name China as a bad actor but, instead, create a high bar for how all companies manage their data. Failure to establish a compelling vision for U.S. internet governance will only allow more space around the world for companies that are controlled by the Chinese Communist Party to flourish worldwide, and Beijing’s vision for the internet with it.




.jpg?sfvrsn=d5e57b75_7)
