The Emergence of Physically Mediated Cyberattacks?
Physical violence against personnel in lawless environments as an element of cyberattack is another dimension of cyber conflict, and its importance has been neglected for way too long.
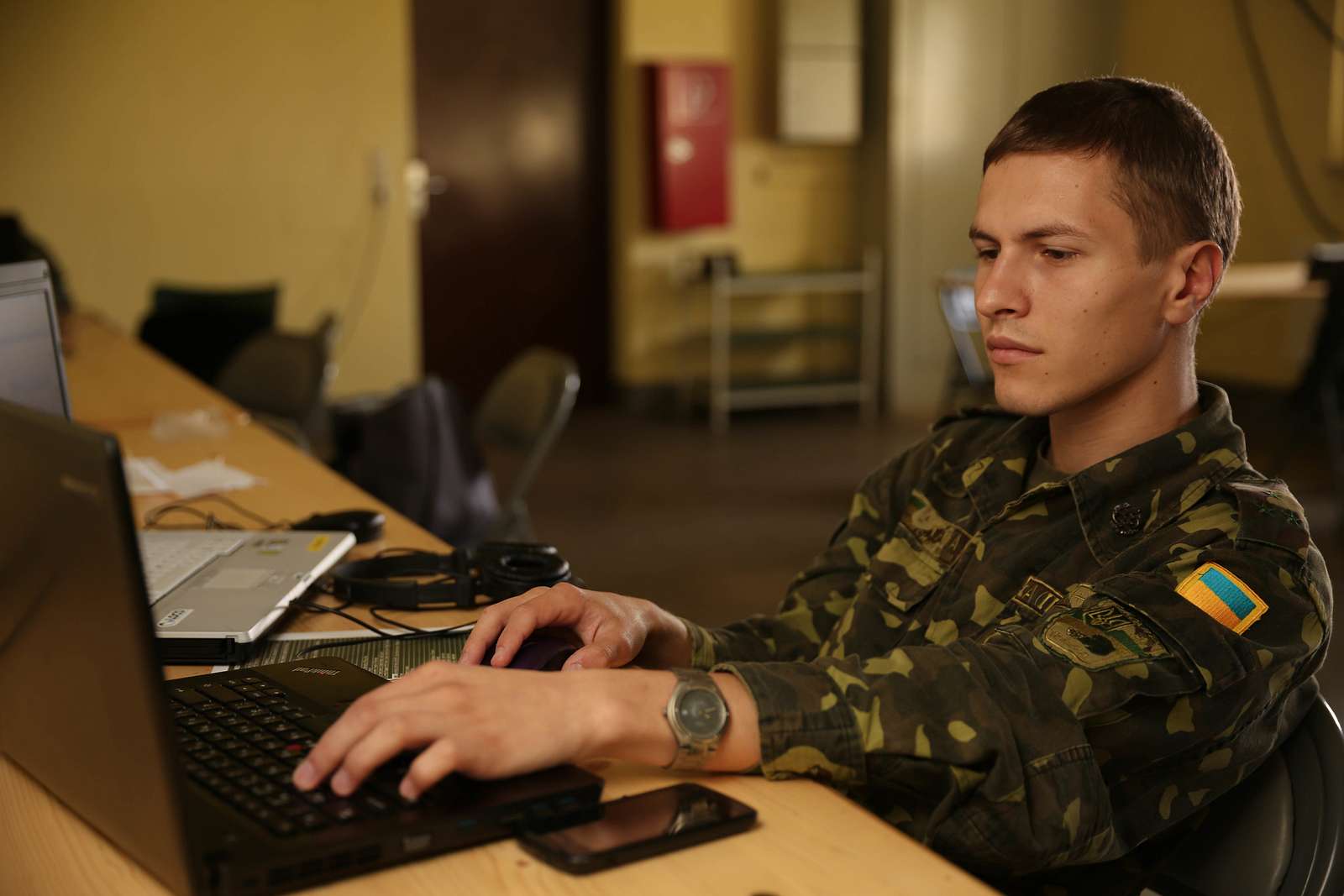
On May 13, the State Service of Special Communication and Information Protection of Ukraine published a notice alleging that “Russia’s special services” are targeting Ukrainian internet service providers (ISPs). If this notice is to be believed, the world has just witnessed a new kind of cyberattack—different in kind rather than in degree. Here’s the relevant part:
Free access to information is a major threat to the enemy in the occupied territories of our country. As long as Ukrainians know about the true course of the war russian propaganda fails.
That is why russia keeps trying to connect Ukrainian Internet service providers to their own system controlled by russia’s special services to block access to Ukrainian web resources and gain a complete control of any activity of Ukrainian users in the Internet. Invaders use every available method, resort to blackmailing and intimidate those who refuse to “collaborate” with the occupants.
This morning, terrorists from the so called russian guard invaded the office of Status, a Kherson-based company, and disconnected all the communication equipment. Now they are blackmailing the company’s management and promise to take away all the equipment if those refuse to connect to the Crimean network.
It seems that the notice was translated into English from another language, probably Ukrainian. But even allowing for translation errors, it appears as though the parties that physically invaded the offices of Stratus, an internet service provider, conducted a physical denial-of-service attack against the telecommunications equipment in the office and sought to alter the availability of websites that users of the service would normally be able to access.
One can imagine that an attacker could cause such outcomes electronically, that is, through various cyberattacks carried across the internet. But to the best of my knowledge, this is the first time that parties wishing to cause such an effect have used an approach based on physical force. A 2009 National Academies report, for which I was co-editor, mentioned in general terms the possibility of such cyberattacks but regretfully did not analyze it in depth. So it is interesting to consider the implications of what might be called physically mediated cyberattacks—attacks that compromise cyber functionality through the use of or the threat of physical force.
Insider attacks are a well-known problem in cybersecurity. In such attacks, trusted (authorized) insiders are “turned” to misuse their privileges, performing actions for which they have the proper technical authorization but for purposes that are contrary to the rationale for granting those authorizations in the first place. Insiders can in principle be turned through a variety of means, including bribery, blackmail, extortion, sexual favors and so on. As importantly, they generally try to keep their activities secret.
The physical facilities of ISPs have also been known to be vulnerable, as exemplified by cuts in fiber-optic cables resulting in denials of service to customers depending on those cables. Documented cases of such cuts point mostly to accidental cuts, but of course there is no reason that some such cuts could not have been made deliberately by parties unknown. Physical security of cyber infrastructure has always been an important, if often neglected aspect of cybersecurity.
But the case described above feels different to me. The office intrusion occurred in Kherson, which was the first city taken by Russian soldiers in the invasion, and the Russia-installed authorities are apparently asking Russia to formally annex the region. While a demand for an ISP located in a region under Russian military occupation to conform to Moscow’s demands regarding internet connectivity is not surprising, one can also imagine similar activities directed against ISPs located in other regions whose governance is contested.
For example, it is not hard to imagine that the chief executive officer of a Ukrainian ISP located in a contested city might receive threats against his family to persuade him to implement certain Russia-friendly changes to the connectivity it provides to its customers. Russians conducting physically enabled cyberattacks need not install malware implants by clandestinely turning an insider. Rather, the soldiers can march with guns into the control center of an ISP and demand that the on-duty personnel plug in a USB drive to install malware that can signal when it is removed—and if it is removed, the children of the chief information security officer are targeted for kidnapping the next day.
Physical violence against personnel in lawless environments as an element of cyberattack is another dimension of cyber conflict, and its importance has been neglected for way too long. We need to start paying more attention to it.





