Jim Comey, ISIS, and "Going Dark"
I had a lengthy conversation with FBI Director Jim Comey today about the nexus of our domestic ISIS problem and what the FBI calls the "going dark" issue. CNN the other day reported on some remarks Comey made on the subject, remarks that have not gotten enough attention but reflect a problem at the front of his mind these days:
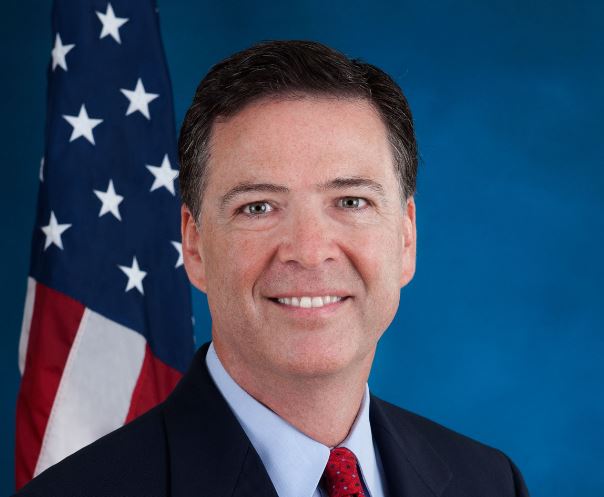
I had a lengthy conversation with FBI Director Jim Comey today about the nexus of our domestic ISIS problem and what the FBI calls the "going dark" issue. CNN the other day reported on some remarks Comey made on the subject, remarks that have not gotten enough attention but reflect a problem at the front of his mind these days:
FBI Director James Comey said Thursday his agency does not yet have the capabilities to limit ISIS attempts to recruit Americans through social media.
It is becoming increasingly apparent that Americans are gravitating toward the militant organization by engaging with ISIS online, Comey said, but he told reporters that "we don't have the capability we need" to keep the "troubled minds" at home.
"Our job is to find needles in a nationwide haystack, needles that are increasingly invisible to us because of end-to-end encryption," Comey said. "This is the 'going dark' problem in high definition."
Comey said ISIS is increasingly communicating with Americans via mobile apps that are difficult for the FBI to decrypt. He also explained that he had to balance the desire to intercept the communication with broader privacy concerns.
"It is a really, really hard problem, but the collision that's going on between important privacy concerns and public safety is significant enough that we have to figure out a way to solve it," Comey said.
Let's unpack this.
As has been widely reported, the FBI has been busy recently dealing with ISIS threats. There have been a bunch of arrests, both because ISIS has gotten extremely good at the inducing self-radicalization in disaffected souls worldwide using Twitter and because of the convergence of Ramadan and the run-up to the July 4 holiday.
As has also been widely reported, the FBI is concerned about the effect of end-to-end encryption on its ability to conduct counterterrorism operations and other law enforcement functions. The concern is two-fold: It's about data at rest on devices, data that is now being encrypted in a fashion that can't easily be cracked when those devices are lawfully seized. And it's also about data in transit between devices, data encrypted such that when captured with a lawful court-ordered wiretap, the signal intercepted is undecipherable. Comey raised his concerns on both subjects at a speech at Brookings last year and has talked about them periodically since then:
What was not clear to me until today, however, was the extent to which the ISIS concerns and the "going dark" concerns have converged. In his Brookings speech, Comey did not focus on counterterrorism in the examples he gave of the going dark problem. In the remarks quoted by CNN, and in his conversation with me today, however, he made clear that the landscape is changing fast. Initial recruitment may take place on Twitter, but the promising ISIS candidate quickly gets moved onto messaging platforms that are encrypted end to end. As a practical matter, that means there are people in the United States whom authorities reasonably believe to be in contact with ISIS for whom surveillance is lawful and appropriate but for whom useful signals interception is not technically feasible.
That's a pretty scary thought.
I don't know what the right answer is to this problem, which involves a particularly complex mix of legitimate cybersecurity, investigative, and privacy questions. I do think the problem is a very different one if the costs of impaired law enforcement access to signal is enhanced ISIS ability to communicate with its recruits than if we're dealing primarily with more routine crimes, even serious ones.
I also think it's an issue that warrants a very serious discussion. This is an issue on which battle lines were drawn more than 20 years ago and a lot of people have lived in the same trenches since then. It's an area that, at least in my view, would benefit a lot from fresh thinking on all sides. Comey has taken a lot of heat for reopening this subject, but I think it's more than fair for him to ask whether we really want ISIS to be able to recruit people on Twitter and then have secure communications with them elsewhere. And if we don't want that, what then?





