Two Americas: Cross-Border Data Requests Post-Dobbs
Following the Supreme Court’s abortion ruling in Dobbs this past June, cross-border data requests between states for abortion-related investigations may start to resemble cross-border requests between countries and trigger new conflicts of law.
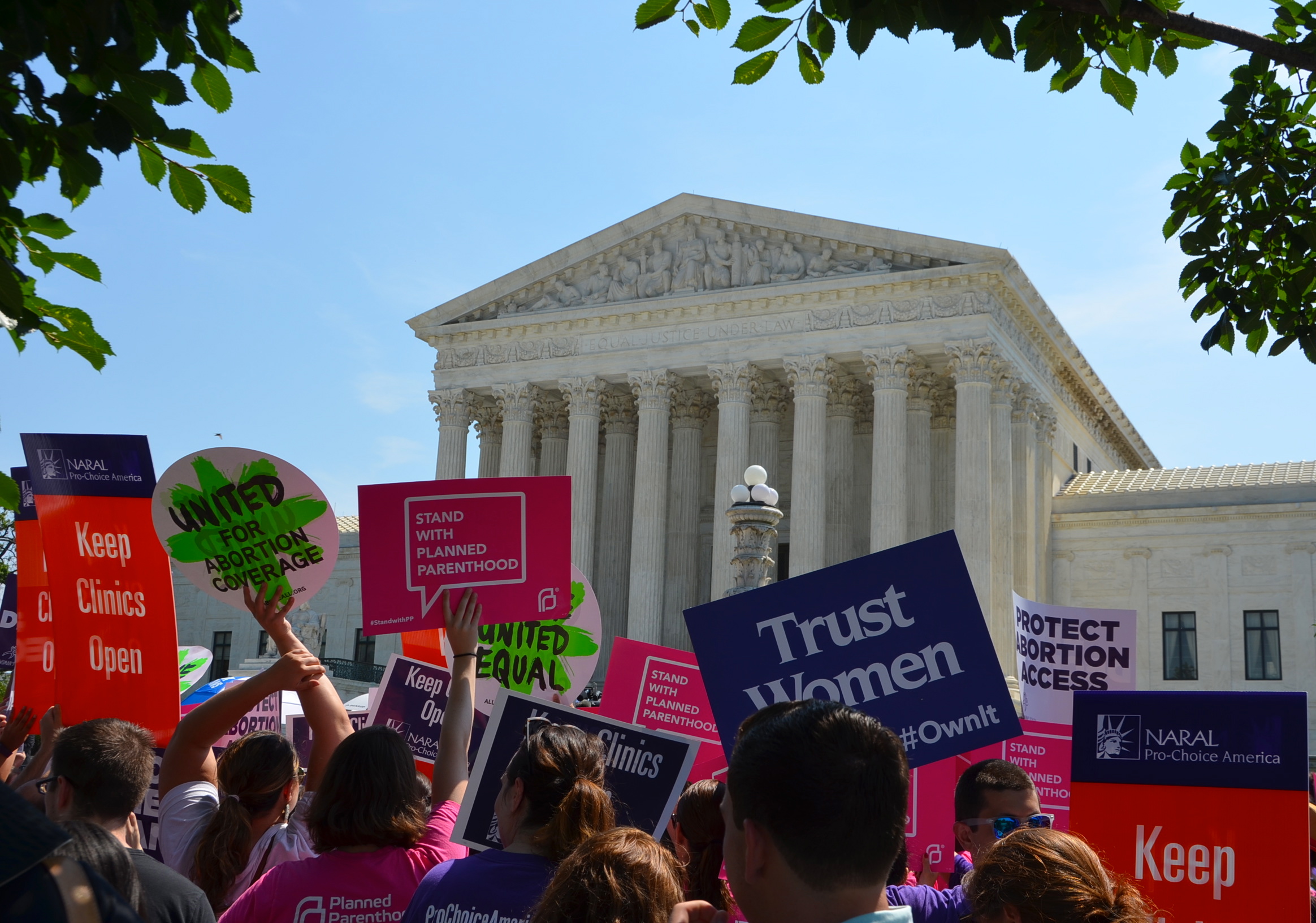
Following the Supreme Court’s decision in Dobbs v. Jackson Women’s Health Organization in June, concerns have been raised by Congress, commentators, and advocacy organizations regarding the ability of state prosecutors to obtain user data as part of a criminal investigation regarding abortions and related services, especially when doing so involves the state compelling the production of out-of-state data. Besides those seeking, aiding, or providing abortions, communications service providers (CSPs) that are subject to the jurisdiction of multiple states also may be understandably concerned about the existing legal framework and their responsibilities under state and federal law.
As part of routine criminal investigations, state and local authorities regularly seek digital evidence from communications service providers, including search history, location information, and the contents of communications and stored files. And while these requests must of course comply with the Fourth Amendment and federal law—most importantly the Electronic Communications Privacy Act (ECPA), which generally governs the ability of CSPs to disclose data to a governmental entity in response to legal process—those constraints are crime-agnostic, in the sense that they do not distinguish between the governmental interests in enforcing different kinds of criminal laws. As such, they likely offer “little or no meaningful protection” against abortion-specific investigations.
But federal law is not the only source of protection. State law can constrain data requests for abortion-related investigations because the CSPs that control the data are often incorporated or physically located outside the border of the requesting state, and demands made of those CSPs therefore implicate another state’s jurisdiction.
Some states, at least historically, have honored these out-of-state (or “foreign” state) requests, either adopting interstate domestication procedures to facilitate cross-border service and enforcement of criminal or civil process or, in some cases, even obligating in-state entities to produce data as if the request were issued under the receiving state’s law. This kind of approach to cross-border demands may make sense in a world where states fundamentally agree on what conduct is criminal. But, following Dobbs, that baseline agreement no longer exists. Instead, there is now a looming specter of evidentiary demands from a state that prohibits abortion (the “criminalizing state”), for an investigation into conduct that is not criminalized by—and perhaps is specifically protected by the public policy, law, and/or constitution of—a state where the data subject, the information, or the provider controlling that information is located (the “protective state”). In this regard, the post-Dobbs world presents an unprecedented scenario for the collection of electronic evidence across state lines, where the compulsory process issued by one state threatens or violates fundamental rights protected in another.
With the rise of these two Americas, it is increasingly likely that protective states will create new barriers against criminalizing-state requests that target the digital privacy of reproductive health decisions and implicate the protective state’s jurisdiction, with California the first state likely to pass such restrictions.
Here, I offer several observations on these kinds of laws. First, I discuss why the part of ECPA that governs requests for stored data—the Stored Communications Act (SCA)—may allow a protective state to impose higher data access standards on cross-border demands from criminalizing states rather than preempt such efforts. Second, I identify parallels from the international setting that provide insight into how protective states might choose to structure these kinds of barriers. Finally, I discuss California’s proposal and the likely conflicts of law that would result from legal changes of this nature.
The SCA: Minimum Federal Standards With State Flexibility
A protective state seeking to enact heightened standards for out-of-state orders will want to account for several additional considerations rooted in federal law, such as the Dormant Commerce Clause and the Full Faith and Credit Clause. Most immediately, however, a protective state would need to grapple with the federal law governing provider disclosures of stored data, the Stored Communications Act—and there is a real question as to whether the SCA explicitly or implicitly preempts such efforts. Express preemption occurs when a federal statute contains language explicitly preempting any state laws; implied preemption exists when a state law frustrates a uniform federal scheme (conflict preemption) or when the federal statute occupies the field of regulation (field preemption). The interaction between the SCA and state law, as seen through a preemption lens, is pivotal to understanding how protective states will be able to protect reproductive health data in the context of cross-border demands.
The SCA is a “blocking” statute. That is, in the absence of an applicable exception, the SCA strictly prohibits a communications service provider from disclosing user data (both the content of a user’s communications and non-content data relating to a user) to a “governmental entity,” including state and local law enforcement. (For simplicity, we can refer to this as the SCA’s “blocking provisions.”)
As an exception to these blocking provisions, the SCA establishes standards that a law enforcement entity must follow to compel the production of user data by a CSP. (We can refer to this as the SCA’s “government access provisions.”) Generally speaking, these standards follow an escalating hierarchy of legal process in accordance with perceived user privacy interests. For example, the SCA requires at least a subpoena for basic subscriber information (such as the subscriber’s name, address, phone number, and billing information); a court order, known as a “D order,” based on a form of heightened suspicion for other non-content records pertaining to a customer (for example, transactional logs and to/from information); and a warrant for the contents of any communications (such as text messages and stored files). The SCA’s government access provisions are in addition to the protections afforded under the Fourth Amendment, which requires a warrant for email content and certain location information.
So how might preemption analysis fare with respect to the SCA? As an initial matter, the SCA contains no express preemption clause. Implied preemption, however, could present more uncertainty, depending on how one views the interaction of the SCA’s blocking and government access provisions and the scope of the relevant state law.
On the one hand, the SCA’s blocking provisions prohibit any disclosures not specified by the statute. For example, the SCA would preempt a state law that ignores these blocking provisions, by authorizing new disclosures that the SCA specifically prohibits; despite the state law, a CSP would still need to comply with the SCA’s restrictions. By the same token, one might argue that the SCA’s blocking provisions similarly preclude a state from imposing any new blocks on provider disclosures. That is, notwithstanding such a state law, a CSP would be free to disclose data in accordance with the SCA.
On the other hand, such state law provisions would not conflict with the SCA’s express limitations on disclosure; rather, they would supplement those privacy protections. This distinction—between conflicting with and supplementing the SCA’s privacy protections—is important because the SCA’s government access provisions (as bolstered by the relevant legislative history) explicitly defer to applicable state processes. And read as a whole, the SCA may allow protective states to raise privacy protections beyond the federal floor. This is illustrated in several ways, detailed below.
First, in seeking the production of data from CSPs for a state investigation, state authorities must undoubtedly comply with the minimum predication thresholds set by the government access provisions. But the statute is clear that state agencies must follow the relevant state procedures when doing so. That is, where the SCA requires a warrant, state agencies must obtain a warrant “issued using State warrant procedures.” Where the SCA requires a subpoena, state agencies must obtain an administrative subpoena “authorized by ... State statute” or a “State grand jury or trial subpoena.” Second, and perhaps more tellingly, where the SCA allows law enforcement to obtain certain non-content information through a newly created D order, the SCA also says state agencies may not obtain a D order if “prohibited by the law of such State.”
In its report accompanying ECPA, the House explained that these requirements “are intended to apply the relevant state law,” and to the extent that a state law or State Constitution imposes a different standard, “then that law would preclude the use of the provisions of this section with respect to state government officials.” The Senate report similarly explained that the federal standards imposed by ECPA do not preempt state laws that impose higher predication for access to data. Notably, the House report also adds that only where federal law enforcement seeks data under the SCA would such elevated state requirements be preempted.
The SCA thus creates a hybrid state-federal model for compulsory process, in which state laws cannot be less protective than the federal statute. For example, a state entity would be prohibited by the SCA (as well as the Fourth Amendment) from using a subpoena for the contents of a user’s communications, or any non-content records other than basic subscriber information. In one such case, the First Circuit held that the SCA preempted a Puerto Rico law requiring disclosure of subscriber information to the government without a subpoena. In contrast, as Congress intended and courts have found, the SCA does not preclude a state’s choice to impose even higher restrictions on disclosure.
To be sure, there is some ambiguity as to which state’s law the SCA is referring to here: the law of the state with jurisdiction over the requesting agency (here, the criminalizing state) or the law of the state with jurisdiction over the provider (here, the protective state). The statutory language could be more readily understood to refer to the former. Nonetheless, the mere fact that the SCA expressly tolerates state laws that add privacy protections leaves plenty of room for protective states to argue against preemption of privacy-protecting laws, at least as applied to demands from another state’s (as opposed to federal) authorities. More broadly, protective states might argue that the SCA as a whole was intended to establish minimal privacy protections, and not to preclude states from augmenting those privacy protections through the creation of new blocking laws or other additional constraints. There is certainly support for those arguments; how they fare remains to be seen.
Potential Models From the International Setting
If protective states can impose heightened standards on abortion-related data, how might they choose to structure these barriers? State officials might look to analogues in international law—such as the Budapest Convention on Cybercrime, mutual legal assistance treaties, and the Clarifying Lawful Overseas Use of Data Act (Cloud Act)—where cross-border access to user data has long been a challenge. To date, nation-states have addressed fundamental differences over the proper scope of cross-border access to evidence through targeted blocking mechanisms, meaning that state-to-state cooperation is generally permitted, except for specific kinds of requests. These kinds of targeted blocking mechanisms illustrate ways in which protective states could seek to impose new barriers of limited scope, while preserving cross-border access elsewhere.
Dual Criminality
Under a “dual criminality” requirement, a country from which evidence is requested is not obligated to transmit such evidence to the requesting country if it is being sought in furtherance of conduct that is not a crime in the requested country. A state could choose to implement a similar kind of restriction, requiring dual criminality for any foreign-state request.
There are two approaches to dual criminality. Under the most restrictive approach, the technical terms or definitions of the criminal offense must be identical. This approach tends to be disfavored because the requirements are rarely satisfied. Under the broader (and favored) approach, the conduct must be subject to criminal prosecution under the law of both countries, even if the elements of those laws are not the same. Article 25 of the Council of Europe’s Budapest Convention on Cybercrime, for instance, adopts the latter approach, as do many mutual legal assistance treaties to which the United States is a party. Sometimes, countries will apply this dual criminality principle in a limited setting. For instance, in the exchange of notes accompanying the 1997 execution of the U.S./U.K. Mutual Legal Assistance Treaty, the parties applied the dual criminality principle by excluding antitrust and competition offenses, which were not enforceable by criminal sanctions in the U.K.
Public Policy and Special Interests
Beyond a dual criminality requirement, international agreements may also preclude information sharing where doing so is contrary to the public policy or special interests of the requested country. For example, the U.S. will refuse cooperation in cases implicating core First Amendment rights, such as political dissidence or critiques of a country’s ruler. And EU countries may choose to withhold cooperation when the case is likely to result in imposition of the death penalty (for example, U.S./EU Extradition Treaty, Article 13). Specific carve-outs like these can be found in Article 27 of the Budapest Convention on Cybercrime, which recognizes the right to refuse cooperation if a country “considers that execution of the request is likely to prejudice its sovereignty, security, ordre public, or other essential interests.” Multiple mutual legal assistance treaties to which the U.S. is a party—such as with France (Article 6) and the U.K. (Article 3)—also include this exception.
Rule of Specialty
International agreements may also impose what is known as a “rule of specialty.” In the context of extradition, the rule of specialty precludes the requesting country from prosecuting an extradited defendant for any crimes other than those identified in an extradition request. In the context of mutual legal assistance, this rule precludes the requesting country from using evidence it obtains for any criminal investigation other than what is specified in the request. As concerns post-Dobbs demands for data, one could imagine a state seeking to impose a restriction on how data produced in response to a foreign-state order may be used, although enforcement of that restriction could present a challenge.
Granted, international instruments typically concern cooperation between nations rather than requests from a government to a CSP. The approaches discussed above may thus work well when protective state authorities are themselves involved in responding to a cross-border legal request. In such cases, state officials would be aptly positioned to evaluate whether a targeted blocking mechanism (such as a dual criminality requirement) is satisfied or if a public policy or special interest exception might be triggered. By comparison, requests made directly to providers would require some translation from the nation-to-nation context.
Certification
This is where countries have opted to employ a certification requirement, as in the Cloud Act. Notwithstanding the SCA’s blocking effect, the Cloud Act permits U.S. CSPs to produce data in response to qualifying requests from a country that has a qualifying bilateral executive agreement with the U.S. But it excludes certain kinds of foreign orders—orders that could infringe freedom of speech and orders that target U.S. persons. As such, the Cloud Act operates in a way that presents a potentially better analogue for states to consider, because a criminalizing state may request abortion-related investigative data directly from a CSP, just as a foreign country’s orders under the Cloud Act are served directly on U.S.-based providers.
To help address this change, the Cloud Act implemented certification requirements. Under the U.S./U.K. agreement (and presumably others to come), requesting authorities must certify in writing that the request “is lawful and complies with [the Cloud Act] agreement” and that the request is being issued under the agreement. These certifications are designed to help providers ascertain whether they must comply with the request and the kinds of objections they may be able to make.
Looking Ahead: New Laws and Legal Conflicts
California’s newly proposed bill, which is expected to be signed by the governor, signals that states are ready to enact these kinds of additional restrictions. And consistent with the varying approaches in the international setting, there are many ways a state could choose to proceed, as the new California law illustrates.
Drawing on principles of dual criminality or public policy, protective states could choose to specifically prohibit, or otherwise impose additional conditions on, abortion-related disclosures by CSPs. This is one approach that California’s proposed law takes: It prohibits the production of records or data by a California CSP when the CSP knows or should know that the warrant or other legal process relates to an abortion investigation by another state. A state might also expand the jurisdictional reach of such a statute to encompass any disclosure of a state resident’s data or a corporation doing business in the state—rather than just the data held by a company incorporated there. California’s law does this too—imposing the new restrictions not just on CSPs incorporated in California but also on CSPs with a principal place of business in California. These restrictions are backed by new civil enforcement powers for the attorney general. To assist CSPs in making a determination about their obligations under the new law, California will also require out-of-state legal process to include an attestation that the records sought do not relate to an abortion investigation, analogous to the Cloud Act’s certification requirements described above.
Other states may soon follow California’s example. Of course, the details of any such laws will matter significantly. So too will the consequences for CSPs, which may be faced with competing legal obligations—required to produce data by the criminalizing state and prohibited from doing so by the protective state.
Here, too, existing practice in the international cross-border context, such as the comity framework codified under the Cloud Act at 18 U.S.C. § 2703(h), offers a model of the kinds of factors that courts might look to when balancing competing state interests. Resolution of those conflicts may ultimately depend on factors such as the physical presence of a provider, the location of the data (if ascertainable), and the identity of the data subject, as well as the relative interests of the respective jurisdictions in the application of their laws. How courts (in addition to which courts) resolve potential conflicts created by competing legal obligations will be especially critical post-Dobbs. States contemplating these kinds of legal changes may want to consider exactly that, as will the CSPs that face this changing legal landscape.




